Ultimate Ethical Hacking Mastery: CEH Pro 2024 Guide
Focused View
12:03:39
001. Certified Ethical Hacker (CEH) Introduction.mp4
01:48
002. Certified Ethical Hacker (CEH) Introduction.mp4
01:48
001. Learning objectives.mp4
00:45
002. 1.1 Introducing Information Security and Cybersecurity.mp4
02:17
003. 1.2 Understanding the Cyber Kill Chain and Hacking Concepts.mp4
07:33
004. 1.3 Surveying Ethical Hacking Methodologies.mp4
11:39
005. 1.4 Undertanding Information Security Controls.mp4
03:03
006. 1.5 Understanding Security Laws and Standards.mp4
03:32
007. 1.6 Planning and Scoping a Penetration Testing Assessment.mp4
05:09
008. 1.7 Building Your Own Hacking Lab with WebSploit Labs.mp4
08:43
001. Learning objectives.mp4
01:25
002. 2.1 Understanding Information Gathering and Vulnerability Identification.mp4
02:27
003. 2.2 Introducing Open Source Intelligence (OSINT) Techniques.mp4
14:39
004. 2.3 Exploring Footprinting Methodologies.mp4
03:12
005. 2.4 Utilizing Search Engines for Footprinting.mp4
05:26
006. 2.5 Footprinting Web Services.mp4
03:55
007. 2.6 Exploiting Social Networking Sites for Footprinting.mp4
01:20
008. 2.7 Surveying Password Dumps, File Metadata, and Public Source-code Repositories.mp4
10:53
009. 2.9 Implementing DNS Footprinting.mp4
03:00
010. 2.10 Executing Network Footprinting.mp4
04:45
011. 2.11 Applying Social Engineering for Footprinting.mp4
03:39
012. 2.12 Introducing Shodan, Maltego, AMass, Recon-NG, and other Recon Tools.mp4
17:34
013. 2.13 Identifying Cloud vs. Self-hosted Assets.mp4
07:13
001. Learning objectives.mp4
00:35
002. 3.1 Surveying Network Scanning Concepts.mp4
06:35
003. 3.2 Exploiting Scanning Tools.mp4
24:34
004. 3.3 Understanding Host Discovery.mp4
08:40
005. 3.4 Performing Website and Web Application Reconnaissance.mp4
10:22
006. 3.5 Performing OS Discovery (Banner GrabbingOS Fingerprinting).mp4
06:08
007. 3.6 Scanning Beyond IDS and Firewall.mp4
12:14
008. 3.7 Creating Network Diagrams.mp4
02:30
009. 3.8 Discovering Cloud Assets.mp4
07:02
010. 3.9 Crafting Packets with Scapy to Perform Reconnaissance.mp4
05:48
001. Learning objectives.mp4
00:20
002. 4.1 Introducing Enumeration Techniques.mp4
01:44
003. 4.2 Performing NetBIOS Enumeration.mp4
02:09
004. 4.3 Performing SNMP Enumeration.mp4
04:39
005. 4.4 Performing LDAP Enumeration.mp4
01:51
006. 4.5 Performing NTP and NFS Enumeration.mp4
03:34
007. 4.6 Performing SMTP and DNS Enumeration.mp4
03:51
008. 4.7 Conducting Additional Enumeration Techniques.mp4
07:40
009. 4.8 Surveying Enumeration Countermeasures.mp4
03:04
001. Learning objectives.mp4
00:30
002. 5.1 Understanding Vulnerability Assessment Concepts.mp4
04:15
003. 5.2 Classifying and Assessing Vulnerability Types.mp4
03:05
004. 5.3 Utilizing Vulnerability Assessment Tools.mp4
03:03
005. 5.4 Generating Vulnerability Assessment Reports.mp4
02:22
001. Learning objectives.mp4
00:58
002. 6.1 Understanding System Hacking Concepts.mp4
01:45
003. 6.2 Gaining System Access.mp4
02:34
004. 6.3 Cracking Passwords.mp4
05:09
005. 6.4 Exploiting Known and Zero-Day Vulnerabilities.mp4
07:32
006. 6.5 Escalating Privileges.mp4
06:09
007. 6.6 Maintaining Access, Command and Control, and Exfiltration.mp4
07:54
008. 6.7 Executing Applications.mp4
08:59
009. 6.8 Hiding Files.mp4
06:31
010. 6.9 Clearing Logs.mp4
04:26
011. 6.10 Performing On-Path Attacks.mp4
05:43
012. 6.11 Introduction to Lateral Movement and Exfiltration.mp4
03:32
013. 6.12 Understanding Post-Engagement Cleanup.mp4
04:22
001. Learning objectives.mp4
00:38
002. 7.1 Understanding Malware Concepts.mp4
02:40
003. 7.2 Comprehending APT Concepts.mp4
02:23
004. 7.3 Grasping Trojan Concepts.mp4
04:12
005. 7.4 Exploring Virus and Worm Concepts.mp4
02:21
006. 7.5 Examining Fileless Malware and Living off the Land Techniques.mp4
04:52
007. 7.6 Analyzing Malware.mp4
05:03
008. 7.7 Implementing Malware Countermeasures.mp4
04:00
001. Learning objectives.mp4
00:28
002. 8.1 Introducing Sniffing Concepts.mp4
12:27
003. 8.2 Performing MAC Attacks.mp4
03:42
004. 8.3 Conducting DHCP Attacks.mp4
05:06
005. 8.4 Performing ARP Poisoning.mp4
04:39
006. 8.5 Performing Spoofing Attacks.mp4
05:59
007. 8.6 Performing DNS Poisoning.mp4
04:54
008. 8.7 Surveying Sniffing Tools.mp4
01:26
009. 8.8 Exploring Sniffing Countermeasures and Detection Techniques.mp4
04:22
001. Learning objectives.mp4
00:35
002. 9.1 Introducing Social Engineering Concepts and Techniques.mp4
03:58
003. 9.2 Understanding the Insider Threat.mp4
05:26
004. 9.3 Impersonation on Social Networking Sites.mp4
04:52
005. 9.4 Understanding Identity Theft.mp4
03:41
006. 9.5 Understanding Social Engineering Countermeasures.mp4
03:38
001. Learning objectives.mp4
00:30
002. 10.1 Introducing DoSDDoS Concepts and Attack Techniques.mp4
07:19
003. 10.2 Defining what are Botnets.mp4
03:02
004. 10.3 Exploring DDoS Case Studies.mp4
02:32
005. 10.4 Surveying DoSDDoS Attack Tools.mp4
02:42
006. 10.5 Understanding DoSDDoS Countermeasures and Protection Tools.mp4
08:34
Read me First.txt
freeeducationweb - link to website.url
freeeducationweb - link to website.zip
001. Learning objectives.mp4
00:30
002. 11.1 Introducing Session Hijacking Concepts.mp4
05:31
003. 11.2 Performing Application Level Session Hijacking.mp4
05:26
004. 11.3 Understanding Network Level Session Hijacking.mp4
06:14
005. 11.4 Surveying Session Hijacking Tools.mp4
02:21
006. 11.5 Understanding Session Hijacking Countermeasures.mp4
03:18
001. Learning objectives.mp4
01:05
002. 12.1 Introducing IDS, IPS, Firewall, and Honeypot Concepts.mp4
05:41
003. 12.2 Exploring IDS, IPS, Firewall, and Honeypot Solutions.mp4
09:14
004. 12.3 Evading IDS and Firewalls.mp4
06:45
005. 12.4 Surveying IDSFirewall Evading Tools.mp4
04:14
006. 12.5 Detecting Honeypots and Sandboxes.mp4
05:02
007. 12.6 Understanding IDSFirewall Evasion Countermeasures.mp4
04:48
001. Learning objectives.mp4
00:29
002. 13.1 Introducing Web Server Concepts.mp4
08:03
003. 13.2 Exploring Web Server Attacks.mp4
08:30
004. 13.3 Surveying Web Server Attack Methodologies.mp4
09:38
005. 13.4 Understanding Web Server Countermeasures.mp4
07:23
006. 13.5 Understanding Patch Management.mp4
13:05
001. Learning objectives.mp4
01:26
002. 14.1 Understanding Web App Concepts and Identifying Web App Threats.mp4
02:35
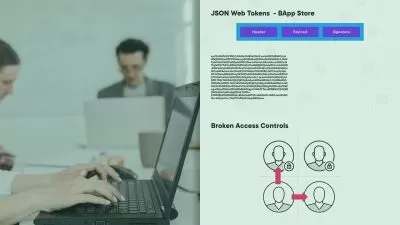
003. 14.2 Exploring the OWASP Top 10 for Web Applications.mp4
06:17
004. 14.3 Applying Web App Hacking Methodologies and Footprinting Web Infrastructure.mp4
04:59
005. 14.4 Analyzing Web Applications and Bypassing Client-Side Controls.mp4
07:43
006. 14.5 Attacking Authentication Mechanisms.mp4
02:07
007. 14.6 Attacking Session Management Mechanisms.mp4
04:30
008. 14.7 Exploiting Authorization Schemes and Access Controls Flaws.mp4
16:14
009. 14.8 Exploiting Cross-site Scripting (XSS) and Cross-site Request Forgery (CSRF) Vulnerabilities.mp4
16:47
010. 14.9 Understanding Server-side Request Forgery (SSRF) Vulnerabilities.mp4
10:06
011. 14.10 Exploiting Buffer Overflows and Creating Payloads.mp4
24:04
012. 14.11 Attacking Application Logic Flaws and Shared Environments.mp4
05:08
013. 14.12 Attacking Database Connectivity and Web App Clients.mp4
04:08
014. 14.13 Attacking Web Services, Exploiting Web APIs, Webhooks, and Web Shells.mp4
11:22
015. 14.14 Ensuring Web App Security.mp4
02:39
001. Learning objectives.mp4
00:40
002. 15.1 Introducing SQL Injection Concepts.mp4
23:02
003. 15.2 Understanding the Types of SQL Injection.mp4
08:09
004. 15.3 Exploring the SQL Injection Methodologies.mp4
10:36
005. 15.4 Exploring SQL Injection Tools.mp4
13:04
006. 15.5 Exploring SQL Injection Evasion Techniques.mp4
03:39
007. 15.6 Understanding SQL Injection Countermeasures.mp4
03:12
More details
Course Overview
Master cybersecurity penetration testing with this comprehensive Certified Ethical Hacker (CEH) course covering footprinting, system hacking, web app vulnerabilities, and advanced defense techniques.
What You'll Learn
- Conduct network scanning and vulnerability analysis
- Execute system hacking and malware analysis
- Defend against social engineering and DDoS attacks
Who This Is For
- Aspiring ethical hackers and penetration testers
- IT professionals enhancing security skills
- Cybersecurity analysts preparing for CEH certification
Key Benefits
- Hands-on labs for real-world hacking scenarios
- Covers latest tools like Shodan, Maltego, and Scapy
- Includes OWASP Top 10 web vulnerabilities
Curriculum Highlights
- Footprinting and Reconnaissance techniques
- System Hacking and Privilege Escalation
- Web Server/Application Penetration Testing
Focused display
Category
- language english
- Training sessions 130
- duration 12:03:39
- Release Date 2025/05/26